A Keylogger, a short form for keystroke logger, is a type of monitoring or digital surveillance tool (software or hardware) that is primarily used to record (log) keyboard keystrokes made by the user of the host computer. They are more advanced in recent times and are sometimes also used to log mouse clicks, touches, etc., typically in a covert manner that ensures the user doesn’t know their actions are being monitored.
While the most popular use of keyloggers is in malicious applications to perpetrate unlawful acts like; collecting personal information like credit card numbers, user names, passwords, etc., legitimate uses for them do exist with, parents using it to monitor their kid’s online activity, ethical hackers/law enforcement agents using it to analyze and track incidents linked to the use of personal computers, and employers using them to ensure employees stay on task.
While software-based keyloggers are more popular because they are less conspicuous, hardware-based keyloggers also have their applications, a good example of which is the employer-employee scenario described above. There are a lot of DIY hardware-based keyloggers on the internet but the recently shared USB WiFi Keylogger by KoKo is one of the most interesting I’ve seen in a while.
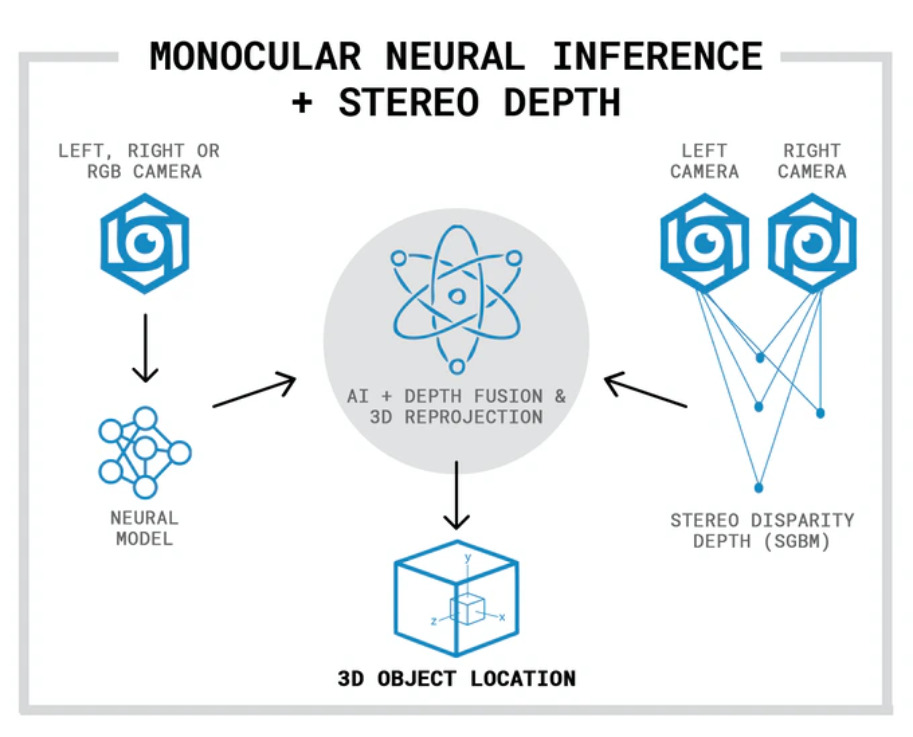
The USB WiFi Keylogger is capable of sniffing keypresses sent from a USB keyboard to a computer and presenting them to the attacker/monitoring entity over WiFi.
The device was designed to be a plug and play device. Simply plug the target USB Keyboard into the female USB port of the keylogger then plug the USB Keylogger into the target computer. After about five seconds, any keys pressed on the keyboard will be logged by the keylogger and passed through to the target computer.
The keylogger is based on the MAX3421EE USB interface and combines an ESP8266 with an Atmega32u4 microcontroller.
To allow external access to the key presses, it is stored in the file system of the ESP8266 which can be accessed over WiFi via the device’s web interface. To access the web interface the monitoring entity needs to be within the range and connected to the WiFi access point created by the USB Keylogger. With this in place, the monitoring entity can navigate to a specified URL and see the logged keypresses displayed withing the textbox on that page. To start a fresh log, the user can clear the previously logged keystrokes using a clear button located at the bottom of the page.
Asides from logging keystrokes, the Masterkey USB WiFi Keylogger can also be used to perform a sort of attack known as Keystroke injection attacks. This can be done via the web interface by navigating to the Live Execute tab at the top of the screen. Through the Live Execute tab, the user can write, run, and save keystroke injection scripts written in ducky script. Users can also save scripts to be used later or upload prewritten scripts to be executed on Masterkey.
For security and customization purposes, the Masterkey has a Settings tab that allows users to customize the appearance of the device and secure the wireless access point. Users are able to change elements like the APN’s SSID, APN’s password, the Channel on which the access point will be broadcasted, and the Hidden elements which will tell the master key whether or not to broadcast the access point.
The Masterkey runs a modified version of spacehuhn’s wifi keylogger code with a few more bells and whistles, and it supports over-the-air firmware update for the ESP8266’s firmware using ElegantOTA.
More information about the Masterkey can be found on the project’s GitHub repo which also holds all the resources you will need to build your own version of the device. KoKo has done quite a lot of work on Hardware keyloggers and you can find more information on diverse kinds of Keyloggers a repo dedicated to them.