Automation is defined as using various control systems to operate equipment such that there is minimal human intervention. Closed control loops (feedback systems) regulate how other systems or devices behave by taking into consideration their output and making corrections based on feedback. An example of this feedback system is Progressive Automation Linear Actuators. In this article challenges of control loops in wireless systems are discussed.
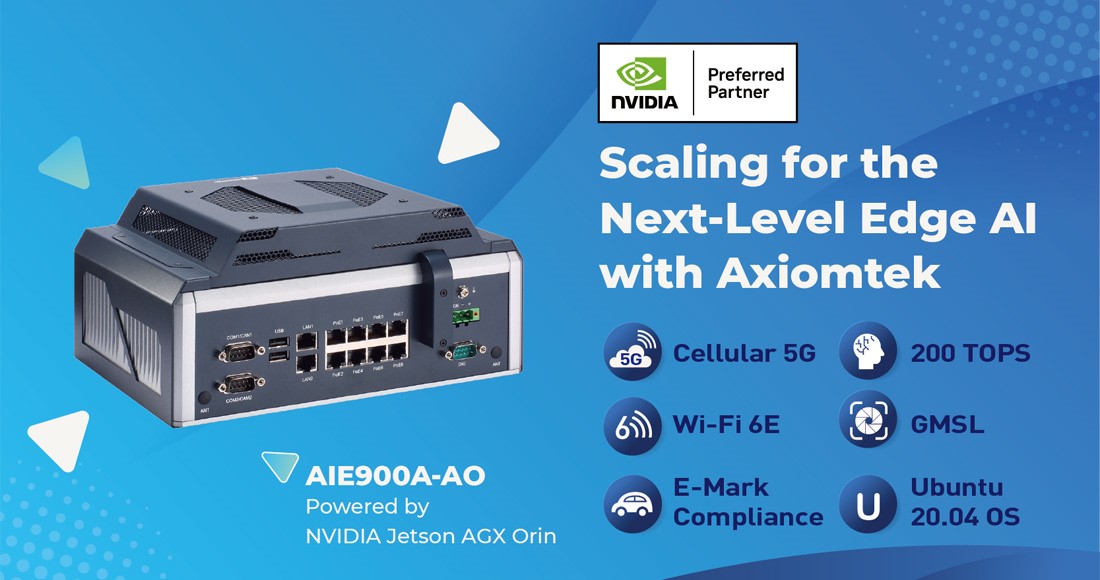
Though embedded modules can be used be used with Wi-Fi, the aim of recent protocols is providing wireless networks with more focused support for control loops. For tight control loops, devices supporting the IEEE802.15.4 ZigBee standard can be used in supporting the recent protocols. Below is a Microchip’s MRF24WB Wi-Fi module.
For sharing a common medium of communication, sensors and controllers are required by a control system that is adopting wireless communication. The network’s quality is a trivial part of the functioning of the overall system when implementing a closed-loop control system using a common communication system.
Earlier short range wireless networks pose a problem since delay deadlines are not used in packet consideration and regardless of these requirements, the packets are treated the same. For a closed loop control system, this presents a major challenge since actuators influencing the system are controlled by the sensor’s data. Data delays lead to negative reinforcement, hence instead of a process being kept within close limits, it runs away.An open loop system, on the other hand, returns analyzed data with changes to a central controller, ordered in minutes or even seconds. In situations or processes that change slowly, the above is used where the process can be brought back easily, is not within its limit or terminated.
The above can be by-passed by having an application use the wireless medium associating every packet with a delay requirement. In a system where a high number of users exist, Wireless Sensor Network simulations done using the IEEE 802.15.4 standard showed a considerable outperformance of the original standards by these mechanisms.
Researchers are looking into using IP technology to be used in wireless networks to provide deterministic control loops. The use of machine-to-machine applications (M2M) has been increasing. In a typical M2M scenario, an anomaly is detected by the sensor then sends to a monitoring middleware an alert that gives information to a business operation software, produces a command for an actuator, and to an operator off the loop, it sends an alarm.
M2M applications need to scalable. This is being made possible by IPV6 that has an address range of 128 bits. It also has neighbor discovery and has improved mechanisms for address allocation and peering. New introductions include unique local Addresses and a provision of a more deterministic environment for supporting control loops.
An additional performance of 802.11 is one use of the above and yields high-performance links, giving more time to elements of the control loop and at the same time utilizing cost-effective hardware, for example, Microchip’s MRF24WB0MA Wi-Fi module. Additionally, layers can be customized, then added to the protocol stack, for the system to be customized for specified control requirements.
In conclusion, closed control loop implementation still poses a challenge. If real-time performance is a major consideration, popular wireless protocols present problems if the architectures are not optimized carefully. Advantages are provided by IPV6 but in providing demanded capabilities for the deterministic network, protocol processor performance has to be improved.